case study returns released for blockworks legacy practice mode can also be completed in blockworks online practice mode. true. false.
Answers
The statement "case study returns released for blockwork legacy practice mode can also be completed in blockwork online practice mode" is true.
What is a case study?A case study is an in-depth examination of a particular subject, such as a person, group, location, occasion, business, or phenomenon. In social, educational, clinical, and business research, case studies are frequently used.
A case study is a type of research methodology that produces a thorough, multifaceted understanding of a complex problem in its actual setting. It is a well-known research strategy that is widely applied in a range of fields, especially the social sciences.
Therefore, the statement is true.
To learn more about the case study, refer to the link:
https://brainly.com/question/24259426
#SPJ1
Related Questions
The router is physically located in a server room that requires an ID card for access. You backed up the router configuration to a remote location in an encrypted file. You access the router configuration interface from your notebook computer using a Telnet client with the username admin and the password admin. You used the MD5 hashing algorithm to protect the password. What should you do to increase the security of this device
Answers
Answer: Use an SSH client to access the router configuration.
Change the default administrative username and password
Explanation:
Based on the information given, in order to increase the security of the device, it's vital to use an SSH client to access the router configuration. The SSH client refers to the program that helps in establishing an authenticated and secure SSH connections to the SSH servers. It's vital for operating network services securely over a network that's unsecured.
Also, the default administrative username and password should be changed to a more secure username and password which can't be easily known by a third party.
In a 100m sprint, identify some of the phases that you would see the athlete complete?
Answers
Answer:
in a 100m sprint identify some of the phases
Question 1:
An output device sends data to a computer.
True
False
Question 2:
An input device receives data from a computer
True
False
Answers
Answer:
1) False
2) False
Explanation:
I don't mean to be rude or anything but, how do you not know the answer to this question? You can even look it up online and you will get an answer.
Input sends data because it goes IN your pc.
Output receives data because it goes OUT of your computer.
List out differences in the ways global communities were formed before and after the advent of the internet and social media.
Answers
Answer:
is a remarkably complex technical system built on the creative contributions of scientists around the world from the 1950s to the present. Throughout its evolution, the Internet and other networks have been promoted by governments, researchers, educators, and individuals as tools for meeting a range of human needs. A combination of high-level policy and grassroots improvisation has produced social benefits including easier and more widespread access to computers and information; increased scientific collaboration; economic growth; the formation of virtual communities and an increased ability to maintain social ties over long distances; the democratization of content creation; and online political and social activism. The Internet’s rapid growth has also spawned technical crises, such as congestion and a scarcity of network addresses, and social dilemmas, including malicious and illegal activities and persistent digital divides based on income, location, age, gender, and education. Such problems continue to demand creative solutions from scientists, policy makers, and citizens.
Several general themes characterize the technical development of the Internet. First, from the 1950s to the present there has been a steady increase in the size of data networks and the variety of services they offer. Rapid growth and diversity have forced network designers to overcome incompatibilities between computer systems and components, manage data traffic to avoid congestion and chaos, and reach international agreement on technical standards. These challenges have led to fundamental advances in research areas such as operating systems and queuing theory. A second trend has been the modeling of network functions as a series of layers, each of which behaves according to a standard protocol, a set of rules for interaction that is implemented in software or hardware. Layering reduces the complexity of the network system and minimizes the amount of standardization necessary, which makes it easier for networks to join the Internet. A third important feature of the Internet’s technical development has been an unusually decentralized and participatory design process. This has opened the system to innovation from a variety of directions and has encouraged informal worldwide collaboration. The following sections describe some of the major milestones in the evolution of the Internet and its predecessors.
another way to express an algorithm is with pseudocode. true or false
Answers
True. Pseudocode is a method of expressing an algorithm using a combination of natural language and programming language-like constructs.
It is not tied to any specific programming language syntax and allows for a more informal and readable representation of an algorithm's logic.
Pseudocode is often used in the early stages of software development as a means of planning and describing the steps and logic of a program before actual coding takes place.
It serves as a communication tool between developers and can be easily understood by both technical and non-technical individuals. Pseudocode typically employs keywords, control structures, and variable names to outline the sequence of operations and decision-making processes within an algorithm.
Its purpose is to provide a clear and concise representation of the algorithm's logic, making it easier to understand and implement in actual code.
learn more about Pseudocode here:
https://brainly.com/question/13208346
#SPJ11
hard disk is a sequential data access medium. true or false?
Answers
My answer is TRUE
Explanation:
Hope it help!!
Hi, can someone please help me with this? I've been having a lot of trouble with it.
The assignment
Your job in this assignment is to write a program that takes a message as a string and reduces the number of characters it uses in two different set ways. The first thing your program will do is ask the user to type a message which will be stored as a String. The String entered should be immediately converted to lowercase as this will make processing much easier. You will then apply two different algorithms to shorten the data contained within the String.
Algorithm 1
This algorithm creates a string from the message in which every vowel (a, e, i, o, and u) is removed unless the vowel is at the very start of a word (i.e., it is preceded by a space or is the first letter of the message). Every repeated non-vowel character is also removed from the new string (i.e., if a character appears several times in a row it should only appear once at that location). So for example the string "I will arrive in Mississippi really soon" becomes "i wl arv in mssp rly sn".
After applying this algorithm, your program should output the shortened message, the number of vowels removed, the number of repeated non-vowel characters removed, and how much shorter the shortened message is than the original message. The exact format in which the program should print this information is shown in the sample runs.
Algorithm 2
This algorithm creates a string by taking each unique character in the message in the order they first appear and putting that letter and the number of times it appears in the original message into the shortened string. Your algorithm should ignore any spaces in the message, and any characters which it has already put into the shortened string. For example, the string "I will arrive in Mississippi really soon" becomes "8i1w4l2a3r1v2e2n1m5s2p1y2o".
After applying this algorithm, your program should output the shortened message, the number of different characters appearing, and how much shorter the shortened message is than the original message. The exact format in which the program should print this information is shown in the sample runs.
Sample Run 1
Type the message to be shortened
This message could be a little shorter
Algorithm 1
Vowels removed: 11
Repeats removed: 2
Algorithm 1 message: ths msg cld b a ltl shrtr
Algorithm 1 characters saved: 13
Algorithm 2
Unique characters found: 15
Algorithm 2 message: 4t2h2i4s1m5e2a1g1c2o1u3l1d1b2r
Algorithm 2 characters saved: 8
Sample Run 2
Type the message to be shortened
I will arrive in Mississippi really soon
Algorithm 1
Vowels removed: 11
Repeats removed: 6
Algorithm 1 message: i wl arv in mssp rly sn
Algorithm 1 characters saved: 17
Algorithm 2
Unique characters found: 13
Algorithm 2 message: 8i1w4l2a3r1v2e2n1m5s2p1y2o
Algorithm 2 characters saved: 14
Milestones
As you work on this assignment, you can use the milestones below to inform your development process:
Milestone 1: Set up a program that takes a string input and converts all the letters to lowercase. Start implementing algorithm 1: create a counter variable and iterate through the characters of the String, incrementing this each time a vowel is encountered which is not preceded by a space or is at the start of the String. So at the end of the loop this counts the number of vowels that are not at the start of a word.
Milestone 2: Add further conditions (using else if) in your loop to count any non-vowel characters which appear immediately after the same character. Make a new empty String to hold the shortened message at the start of the code, then add a final else condition in the loop to add all characters which were not vowels or repeated letters to this String. Then print the statements for algorithm 1 using your counts and shortened message.
Milestone 3: Start implementing algorithm 2 by writing code that iterates through the String and checks that each character is not a space and has not already appeared in the word before that point. You will need to use nested loops - an outer loop to iterate through the String characters and an inner loop that looks through the previous characters up to that point - and a flag variable to record if a letter was found in the inner loop. Use a counter variable to count all such "unique" characters in the String.
Milestone 4: Add a second inner loop inside the outer loop from the previous which counts all appearances of a character that passes the tests from milestone 3. Add the character and the number of times it appears to another shortened message String (which should start as blank String). Finally, print the statements for algorithm 2 using your unique character count and shortened message.
Answers
Answer:
Scanner scan = new Scanner(System.in);
System.out.println("Type the message to be shortened");
String msg = scan.nextLine();
System.out.println();
msg = msg.toLowerCase();
String newStr = "";
System.out.println("Algorithm 1");
int vowels = 0;
int repeats = 0;
for(int i = 0; i < msg.length(); i++)
{
if((msg.substring(i, i +1).equals("a") || msg.substring(i, i+1).equals("e") || msg.substring(i, i +1).equals("i") || msg.substring(i, i+1).equals("o") || msg.substring(i, i +1).equals("u")))
{
if(i != 0 && !msg.substring(i -1, i).equals(" "))
{
vowels++;
}
else
newStr += msg.substring(i, i +1);
}
else if(i != 0 && msg.substring(i, i +1).equals(msg.substring(i -1, i)))
{
repeats++;
}
else
{
newStr += msg.substring(i, i +1);
}
}
System.out.println("\nAlgorithm 1");
System.out.println("Vowels removed: " + vowels);
System.out.println("Repeats removed: " + repeats);
System.out.println("Algorithm 1 message: " + newStr);
System.out.println("Algorithm 1 characters saved: " + (vowels + repeats));
algorithm2(msg);
}
public static void algorithm2(String msg)
{
String alg2Msg = "";
int uniqueLetters = 0;
// Iterate through each letter in msg
for(int i=0; i < msg.length(); i++)
{
String ltr = msg.substring(i,i+1);
// Only process if this character is not a space
if(!ltr.equals(" "))
{
/* Check whether this character has already appeared by
* iterating through characters from start up to the current
* letter and using a boolean flag variable.
*/
boolean alreadyUsed = false;
for(int j=0; j<i; j++)
{
if(msg.substring(j,j+1).equals(ltr))
{
alreadyUsed = true;
}
}
/* If this character hasn't already appeared,
* iterate through the rest of the characters
* and count how many times it appears.
*/
if(!alreadyUsed)
{
uniqueLetters++;
int count = 0;
for(int j=i; j<msg.length(); j++)
{
if(msg.substring(j,j+1).equals(ltr))
{
count++;
}
}
alg2Msg += count + ltr;
}
}
} //end for loop
System.out.println("\nAlgorithm 2");
System.out.println("Unique characters found: " + uniqueLetters);
System.out.println("Algorithm 2 message: " + alg2Msg);
System.out.println("Algorithm 2 characters saved: " + (msg.length() - alg2Msg.length()));
} //end algorithm2
}
Explanation:
Here you go!
Describe the use of the source and destination ports in both UDP or TCP packets in a request for a service 3. Describe the use of the source and destination ports in both UDP or TCP packets in a response back to the client.
Answers
In both UDP and TCP packets, the source and destination ports are used to identify the endpoints of a communication session.
When a client sends a request for a service, it includes the source port, which is a randomly generated port number used by the client to receive the response back. The destination port, on the other hand, is a well-known port number associated with the specific service being requested.In TCP, once the request packet is sent, the client waits for a response packet to come back to the same source port it used in the request. This ensures that the response is directed to the right client. In UDP, the source port is still used for the same purpose, but the lack of a connection-oriented protocol means that there is no guarantee that the response will arrive or in what order.When the server receives the request packet, it uses the destination port to identify the specific service being requested and routes the request accordingly. Once the service has been provided, the server sends a response packet back to the client's source port, with the server's port number as the destination port. This ensures that the response packet is sent to the correct client, which can then process the response and complete the service request.
learn more about TCP here:
https://brainly.com/question/29349524
#SPJ11
Here are a few elements of breaking news and a feature story. Match the elements of breaking news and a feature story with their correct images.

Answers
Breaking News:
➡️Highlights key events
➡️Answers some, but not necessarily all questions, such as when, where, who, why, and how.
Feature Story:
➡️ No urgency to be reported
➡️Adequate time for research
➡️Includes reviews and Q&A type interviews
➡️Summary lead is the most traditional form often used to create a script
Explanation:
Breaking news is known as a special report or news which reports something current and urgent. It usually interrupts a scheduled program or current news. It answers some questions on the news that just broke out.
Feature story is known to be a news that is non-fiction. It is also known to be a type of soft news. It includes Q&A interviews and reviews. It takes adequate time for research.
Breaking News
Highlights Key eventsIncludes Reviews and Q&A type interviewsAdequate time for researchFeature story
Answers some , but not necessarily all questions , such as when , where , who , why , and howNo urgency to be reportedSummary lead is the most traditional form often used to create a script.
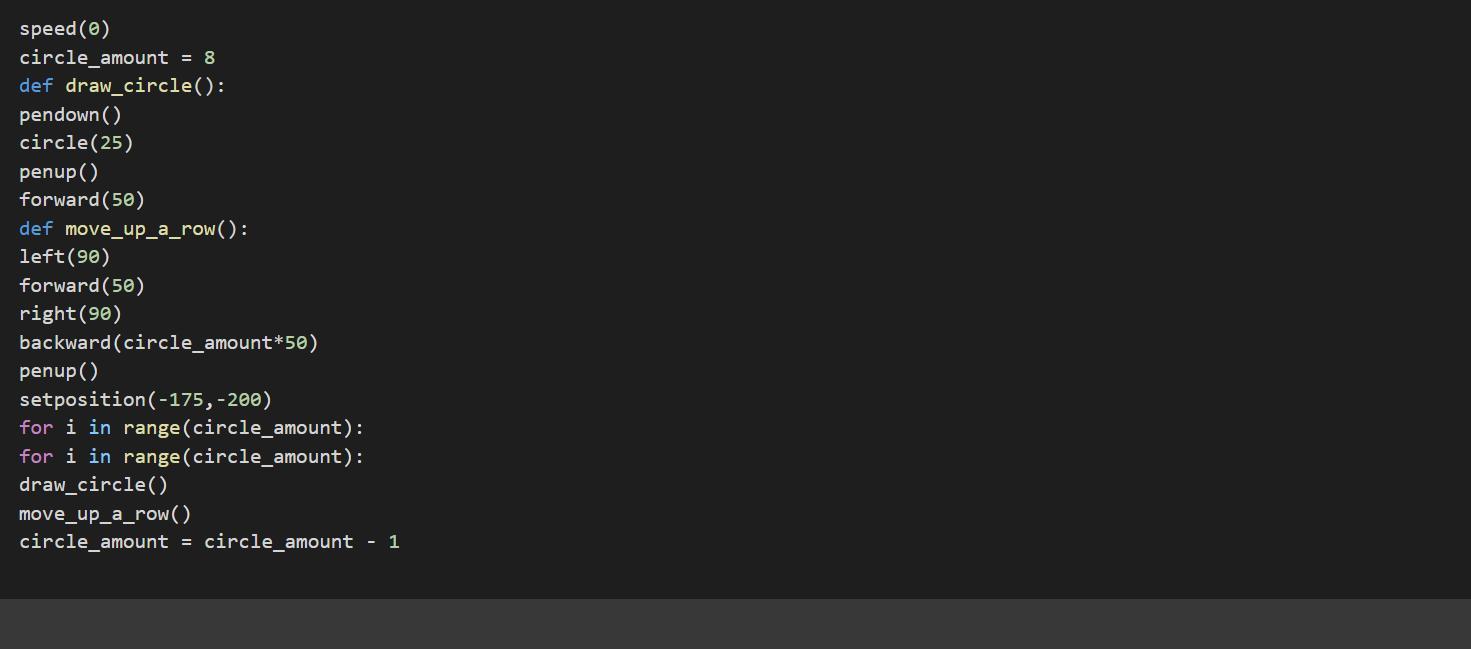
Need answer to 13.1.1 codehs

Answers
Using the knowledge in computational language in python it is possible to write a code that have to make a half pyramid out of circle's need to have a function, a variable named circle_amount.
Writting the code:speed(0)
circle_amount = 8
def draw_circle():
pendown()
circle(25)
penup()
forward(50)
def move_up_a_row():
left(90)
forward(50)
right(90)
backward(circle_amount*50)
penup()
setposition(-175,-200)
for i in range(circle_amount):
for i in range(circle_amount):
draw_circle()
move_up_a_row()
circle_amount = circle_amount - 1
See more about python at brainly.com/question/19705654
#SPJ1
steven is called to fix a network that is experiencing traffic congestion issues. which device should he replace to alleviate these issues
Answers
Answer:
Steven should replace the router to alleviate the traffic congestion issues.
Explanation:
A box has a mass of 5 kg. What is the weight of the box on Earth?
Show your work
Answers
Answer:
5 kg
Explanation:
5 kg
how can you reformat a drive from fat32 to ntfs without losing the existing data
Answers
Reformatting a drive from FAT32 to NTFS without losing existing data can be achieved using the built-in Windows tools. Its recommended to back up data before starting.
To reformat a drive from FAT32 to NTFS without data loss, you can follow these steps:
1. Open the command prompt as an administrator.
2. Type the command "convert drive_letter: /fs:ntfs" and press Enter. Replace "drive_letter" with the actual letter assigned to the drive you want to reformat (e.g., convert C: /fs:ntfs).
3. Confirm the conversion by typing "Y" and pressing Enter.
4. The conversion process will begin, and you will see a progress indicator.
5. Once the conversion is complete, you can close the command prompt. During the conversion process, the file system is changed from FAT32 to NTFS while preserving the existing data on the drive. The conversion takes place without reformatting the drive or deleting any files. However, it's crucial to note that unforeseen issues or errors during the conversion process can result in data loss, so it's always recommended to create a backup of important files before proceeding.
learn more about back up here:
https://brainly.com/question/31916562
#SPJ11
i need help with Mikhail is working in an IDE and needs to test a program one step at a time to find and fix errors. What tool should he use?
Answers
Note that where Mikhail is working in an IDE and needs to test a program one step at a time to find and fix errors he should use a deb. ugger.
What is a deb. ugger?A deb. ugger, often known as a deb. ugging tool, is a computer software that is used to test and deb. ug other programs. A deb. ugger's primary job is to execute the target program under controlled settings, allowing the programmer to trace its execution and monitor changes in computer resources that may reveal faulty code.
A deb. ugger is a software tool that can aid in software development by detecting code problems at various phases of operating system or application development. Some deb. uggers will examine a test run to determine which lines of code did not execute.
Learn more about deb. ugger:
https://brainly.com/question/30502603
#SPJ1
Let x = ["Red", 2.55,"Green", 3,"Black","false"], then solve the following:
1. The output of print(x) is
2. The output of print(len(x)) is
3. The output of print(x[10]) is
4. The output of print(x[1]+x[3]) is
Answers
Answer:
Print(x) would be directly calling the x variable so it would print everything but the []Print(x[10]) is calling the number 10 which results in E2 + d= 2dYou can enter numbers in the Zoom field to zoom in or out a precise amount. True or false
Answers
what do i do for this not to stop me from trying to ask a question. / What phrases are / could be hurtful to brainly? - Don't use such phrases here, not cool! It hurts our feelings :(
Answers
Question #3
Dropdown
Complete the code.
Your program is saved in a folder. The file, "books.txt," is stored in a subfolder named "files."
How do you open the data file to add more data to the existing file?
Answers
The program is an illustration of file manipulations
What are file manipulations?File manipulations are program statements that are used to perform several operations on data files, directories and folders
The program statementThe program in Python, where comments are used to explain each line is as follows:
#This gets the file path of the file "books.txt"
path = 'files\\books.txt'
#This opens the file in append mode
file=open(path, "a")
Read more about file manipulation at:
https://brainly.com/question/15683939
Answer:
A. aFile = open("files/books.txt","a")
Explanation:
Comment above was correct
Your program will read in an existing text file. You want the program to terminate if the file does not exist. Which of the following indicates the correct code for the main method header? public static void main(String[] args) throws FileNotFoundException public static void main(String[] args) throws UnknownFileException public static void main(String[] args) public static void main(String[] args) throws FileMissingException
Answers
Answer:
FileNotFoundException
Explanation:
Which NEC article covers branch circuits?
Answers
Answer:
Explanation:
Article 210
m. goldshtein and p. tsiotras, "finite-horizon covariance control of linear time-varying systems," in proc. ieee conf. decis. control, melbourne, vic, australia, dec. 2017, pp. 3606–3611.
Answers
The main answer to your question is that the paper titled "Finite-horizon Covariance Control of Linear Time-Varying Systems" was authored by M. Goldshtein and P. Tsiotras. It was published in the Proceedings of the IEEE Conference on Decision and Control in Melbourne, VIC, Australia in December 2017. The paper can be found on pages 3606-3611.
Explain the difference between undecidable problems and unreasonable time algorithms. Be specific.
Answers
One for which no algorithm can ever be written to find the solution is an unsolvable problem. An undecidable problem is one for which no algorithm can ever be written that will always provide any input value with a correct true/false option.
An insoluble issue is one for which there is no algorithm that can ever be constructed to locate the solution. Undecidable problems are those for which there is no method that will ever be developed that can consistently return a true/false answer for any input value.
What is time algorithms?If the value of an algorithm is constrained by a value that is independent of the amount of the input, the algorithm is said to be constant time sometimes written as time. For instance, accessing any individual element in an array requires a constant amount of time because just one operation is required to find it.
We employ a technique known as "Big O notation" to describe how time-consuming a method is. We employ a language called the Big O notation to express how time-consuming an algorithm is.
Therefore, we would argue that the insertion sort's best-case time complexity is O. (n). Linear complexity is another name for O(n) complexity.
Thus, An insoluble issue is one for which there is no algorithm.
For more information about time algorithms, click here:
https://brainly.com/question/14635830
#SPJ6
PLEASE HELP!!!
The unit talks about various astronomical tools, but satellites don’t make the list—why? Explain how satellites help us learn more about the Earth from space and analyze whether they can also help us learn more about space.
Answers
Answer:
The bird's-eye view that satellites have allows them to see large areas of Earth at one time. This ability means satellites can collect more data, more quickly, than instruments on the ground.
Explanation:
briefly explain the emerging trends in micro computer technology according to size
Answers
Answer:
Emerging trends in IT include big data analytics, virtual and augmented reality, 5G, and the internet of things. Computer science workers can learn about computer science current events and new technologies by joining a professional organization.Mar 3, 2022
How did imperialism lead to WWI? A The debate of the morality of imperialism created tensions around Europe b Native people were conquered and rebelled against Europe c Europe went into an economic depression when imperialism failed d European nations competed and made alliances to control colonies
Answers
Answer:
d. European nations competed and made alliances to control colonies.
Explanation:
The world War I was a period of battle between various countries from 1914 to 1918. It started formally on the 28th of July, 1914 and ended on the 11th of November, 1918.
Imperialism can be defined as a policy, ideology, or advocacy that sought to extend a country's power, dominion, authority and influence over another country through diplomacy, use of military force or colonization (direct territorial acquisition).
This ultimately implies that, imperialism is an advocacy or policy that is typically used to impose or extend a country's power, dominion, authority and influence. It simply means to seek colonies of other nations or countries.
Hence, imperialism led to WW1 because European nations competed and made alliances to control colonies.
In conclusion, there was an eagerness on the part of European Nations to gain colonial territories that were owned by other rival nations.
Benefits of ansi-sparc architecture for database designers and database developers
Answers
Answer:The ANSI-SPARC architecture is a widely accepted standard for database design and development. It offers numerous benefits to both designers and developers, making it an ideal choice for any organization looking to build a robust and efficient database system.
One of the key advantages of ANSI-SPARC architecture is its flexibility. It allows designers to create data models that can be easily modified or updated as per changing business requirements. This means that organizations can adapt quickly to new market trends or customer demands without having to overhaul their entire database system.
Another benefit of ANSI-SPARC architecture is its scalability. It enables developers to build databases that can handle large volumes of data, ensuring that the system remains performant even as the organization grows in size and complexity.
Moreover, ANSI-SPARC architecture promotes data independence, which means that changes made to one part of the database do not affect other parts. This ensures consistency and accuracy across all aspects of the system.
In conclusion, adopting ANSI-SPARC architecture for database design and development provides numerous benefits such as flexibility, scalability, and data independence. Therefore, it is highly recommended for organizations looking to build a reliable and efficient database system.
Explanation:
ms. danvers is designing a set of virtual machines for her company, miracle. currently, her host machine uses lvm but only has enough disk space for 1 tb of data. her three vms will need 200 gb of disk space immediately but are projected to grow to 300 gb each within the next year. what should she do?
Answers
Ms. Danvers has a task ahead of her in designing a set of virtual machines for Miracle, her company. She has already identified that her host machine uses LVM but only has enough disk space for 1 TB of data. This implies that she needs to be prudent with the space allocation for the virtual machines.
Considering that her three virtual machines require a total of 200 GB of disk space immediately, Ms. Danvers has a few options. One option is to allocate all the space available to the virtual machines and then expand the disk space as the VMs grow. However, this may not be practical, given that the VMs will grow to 300 GB each within the next year, and this could result in insufficient space. Another option is to split the available space into smaller partitions, but this may not be ideal since she may end up with unused disk space on one or more VMs.
Ms. Danvers may also consider using a cloud-based solution, which would provide scalability and flexibility in terms of disk space. Cloud providers often offer scalable and customizable disk space options, allowing Ms. Danvers to adjust the disk space according to her company's needs. This option may, however, come with added costs, depending on the service provider.
In conclusion, Ms. Danvers needs to consider her options carefully before designing the virtual machines. She should look for ways to optimize the disk space available, while also ensuring that there is room for growth in the future. The cloud-based solution is a viable option to consider, although she needs to weigh the costs against the benefits it provides.
Learn more about designing here:
https://brainly.com/question/30225107
#SPJ11
how many games are in the game catalogue on the middle tier of playstation plus
Answers
The middle tier of PlayStation Plus, which is the standard subscription, offers at least two free games per month.
What is game catalogue?The Game Catalog works similarly to Game Pass in that games are added and removed from the service over time.
While the Game Catalog does not provide new, first-party Sony games the day they are released, its library is excellent.
The PlayStation Plus Game Catalog contains up to 400 titles, each jam-packed with new gaming experiences, genres to explore, and vibrant online communities to join.
The standard PlayStation Plus subscription's middle tier includes at least two free games per month.
Thus, there can be several games in the game catalogue on the middle tier of PlayStation plus.
For more details regarding game catalogue, visit:
https://brainly.com/question/30841534
#SPJ1
_____ are identification tags that websites drop on personal-computer hard drives so they can recognize repeat visiters the next time they visit their web sites
Answers
Cookies are identification tags that websites drop on personal-computer hard drives so they can recognize repeat visitors the next time they visit their web sites.
Cookies are small text files that websites send to a user's browser and store on their hard drive. These files contain information such as user preferences, login credentials, and browsing activity. When a user revisits a website, the website retrieves the cookie from the user's hard drive, allowing it to remember the user's previous interactions and personalize their experience.
Cookies serve various purposes, including maintaining user sessions, remembering language preferences, and providing targeted advertising. However, it is important to note that while cookies are generally harmless, they can also be used for tracking and profiling purposes, raising privacy concerns. Most modern web browsers provide options to manage and delete cookies, giving users control over their cookie settings. It is advisable to review and adjust cookie settings according to individual preferences to balance convenience and privacy.
To learn more about Website visit:
https://brainly.com/question/1631583
#SPJ11
what is the fullform of ETA in computer term
Answers
Answer:
Estimated Time of Arrival.